Cisco Certification Exam Prep Materials
Cisco CCNA Exam Prep Material Download
Cisco CCT Exam Prep Material Download
- Cisco 010-151 Dumps PDF
- Cisco 100-490 Dumps PDF
- Cisco 100-890 Dumps PDF
- Tips: Beginning February 10, the CCT Certification 500-150 FLDTEC v1.0 exam will replace the 100-490, 010-151, and 100-890 exams.
Cisco CyberOps Exam Prep Material Download
Cisco DevNet Exam Prep Material Download
Cisco CCNP Exam Prep Material Download
- Cisco 300-410 Dumps PDF
- Cisco 300-415 Dumps PDF
- Cisco 300-420 Dumps PDF
- Cisco 300-425 Dumps PDF
- Cisco 300-430 Dumps PDF
- Cisco 300-435 Dumps PDF
- Cisco 300-440 Dumps PDF
- Cisco 300-510 Dumps PDF
- Cisco 300-515 Dumps PDF
- Cisco 300-535 Dumps PDF
- Cisco 300-610 Dumps PDF
- Cisco 300-615 Dumps PDF
- Cisco 300-620 Dumps PDF
- Cisco 300-630 Dumps PDF
- Cisco 300-635 Dumps PDF
- Cisco 300-710 Dumps PDF
- Cisco 300-715 Dumps PDF
- Cisco 300-720 Dumps PDF
- Cisco 300-725 Dumps PDF
- Cisco 300-730 Dumps PDF
- Cisco 300-735 Dumps PDF
- Cisco 300-810 Dumps PDF
- Cisco 300-815 Dumps PDF
- Cisco 300-820 Dumps PDF
- Cisco 300-835 Dumps PDF
Cisco CCIE Exam Prep Material Download
- Cisco 350-401 Dumps PDF
- Cisco 350-501 Dumps PDF
- Cisco 350-601 Dumps PDF
- Cisco 350-701 Dumps PDF
- Cisco 350-801 Dumps PDF
Cisco CCDE Exam Prep Material Download
Cisco Other Exam Prep Material Download
- Cisco 500-052 Dumps PDF
- Cisco 500-210 Dumps PDF
- Cisco 500-220 Dumps PDF
- Cisco 500-420 Dumps PDF
- Cisco 500-442 Dumps PDF
- Cisco 500-444 Dumps PDF
- Cisco 500-470 Dumps PDF
- Cisco 500-490 Dumps PDF
- Cisco 500-560 Dumps PDF
- Cisco 500-710 Dumps PDF
- Cisco 700-150 Dumps PDF
- Cisco 700-750 Dumps PDF
- Cisco 700-760 Dumps PDF
- Cisco 700-765 Dumps PDF
- Cisco 700-805 Dumps PDF
- Cisco 700-821 Dumps PDF
- Cisco 700-826 Dumps PDF
- Cisco 700-846 Dumps PDF
- Cisco 700-905 Dumps PDF
- Cisco 820-605 Dumps PDF
Fortinet Exam Dumps
fortinet nse4_fgt-6.4 dumps (pdf + vce)
fortinet nse4_fgt-6.2 dumps (pdf + vce)
fortinet nse5_faz-6.4 dumps (pdf + vce)
fortinet nse5_faz-6.2 dumps (pdf + vce)
fortinet nse5_fct-6.2 dumps (pdf + vce)
fortinet nse5_fmg-6.4 dumps (pdf + vce)
fortinet nse5_fmg-6.2 dumps (pdf + vce)
fortinet nse6_fml-6.2 dumps (pdf + vce)
fortinet nse6_fnc-8.5 dumps (pdf + vce)
fortinet nse7_efw-6.4 dumps (pdf + vce)
fortinet nse7_efw-6.2 dumps (pdf + vce)
fortinet nse7_sac-6.2 dumps (pdf + vce)
fortinet nse7_sdw-6.4 dumps (pdf + vce)
fortinet nse8_811 dumps (pdf + vce)
Category: CCNA Security
Download Latest Cisco 210-260 Dumps
QUESTION 4
According to Cisco best practices, which three protocols should the default ACL allow on an access port to enable wired BYOD devices to supply valid credentials and connect to the network? (Choose three.)
A. BOOTP
B. TFTP
C. DNS
D. MAB
E. HTTP
F. 802.1x
Correct Answer: ABC
QUESTION 5
Which two next-generation encryption algorithms does Cisco recommend? (Choose two.)
A. AES
B. 3DES
C. DES
D. MD5
E. DH-1024
F. SHA-384
Correct Answer: AF
QUESTION 6
Which three ESP fields can be encrypted during transmission? (Choose three.)
A. Security Parameter Index
B. Sequence Number
C. MAC Address
D. Padding
E. Pad Length
F. Next Header
Correct Answer: DEF
QUESTION 7
What are two default Cisco IOS privilege levels? (Choose two.)
A. 0
B. 1
C. 5
D. 7
E. 10
F. 15
Correct Answer: BF
QUESTION 8
Which two authentication types does OSPF support? (Choose two.)
A. plaintext
B. MD5
C. HMAC
D. AES 256
E. SHA-1
F. DES
Correct Answer: AB
QUESTION 9
Which two features do CoPP and CPPr use to protect the control plane? (Choose two.)
A. QoS
B. traffic classification
C. access lists
D. policy maps
E. class maps
F. Cisco Express Forwarding
Correct Answer: AB
Cisco 210-260 Exam Materials, Latest Cisco 210-260 Practice Exam Are Based On The Real Exam
Welcome to download the newest Pass4itsure 210-260 Practice Exam VCE dumps: https://www.pass4itsure.com/210-260.html
Through the Cisco 210-260 exam is not easy. Juniper select the appropriate Cisco 210-260 exam sample questions only guarantee of Pass4itsure success. I heard our customers talking about research, but he did not to cram, but told me to go pass4itsure this site with many on Cisco 210-260 exam sample questions, passuitsure can provide relevant research and practical experience in a wide range of foundation. pass4itsure always designs our materials for exams with one goal in mind – ease of use. Through our Cisco 210-260 exam sample questions, we give you a very comfortable environment to study for the exam. We let you know about every detail and also let you analyze your strong and weak Juniper areas. You can then sharpen your skills very quickly and concentrate more on your weaker topics.
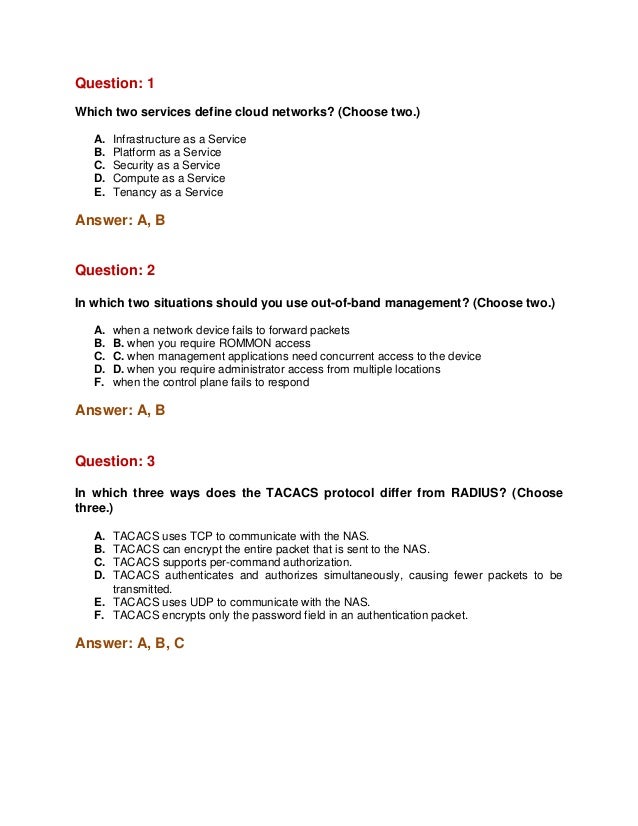
QUESTION 1
Which two services define cloud networks? (Choose two.)
A. Infrastructure as a Service
B. Platform as a Service
C. Security as a Service
D. Compute as a Service
E. Tenancy as a Service
Correct Answer: AB
QUESTION 2
In which two situations should you use out-of-band management? (Choose two.)
A. when a network device fails to forward packets
B. when you require ROMMON access
C. when management applications need concurrent access to the device
D. when you require administrator access from multiple locations
E. when the control plane fails to respond
Correct Answer: AB
QUESTION 3
In which three ways does the TACACS protocol differ from RADIUS? (Choose three.)
A. TACACS uses TCP to communicate with the NAS.
B. TACACS can encrypt the entire packet that is sent to the NAS.
C. TACACS supports per-command authorization.
D. TACACS authenticates and authorizes simultaneously, causing fewer packets to be transmitted.
Cisco 640-554 Cert Exam, Most Popular Cisco 640-554 Dump UP To 50% Off
Welcome to download the newest Pass4itsure 640-554 VCE dumps: https://www.pass4itsure.com/640-554.html
Amazing,100% candidates have pass the Cisco 640-554 exam by practising the preparation material of Flydumps,beacuse the brain dumps are the latest and cover every aspect of Cisco 640-554 eaxm.Download the brain dumps for an undeniable success in Cisco 640-554 exams.
QUESTION 1
Which two features are supported by Cisco IronPort Security Gateway? (Choose two.)
A. Spam protection
B. Outbreak intelligence
C. HTTP and HTTPS scanning
D. Email encryption
E. DDoS protection
Correct Answer: AD Explanation
Explanation/Reference:
http://www.cisco.com/en/US/prod/collateral/vpndevc/ps10128/ps10154/data-sheet-c78- 729751.html
Product Overview Over the past 20 years, email has evolved from a tool used primarily by technical and research professionals to become the backbone of corporate communications. Each day, more than 100 billion corporate email messages are exchanged. As the level of use rises, security becomes a greater priority. Mass spam campaigns are no longer the only concern. Today, spam and malware are just part of a complex picture that includes inbound threats and outbound risks. Cisco. Email Security solutions defend mission-critical email systems with appliance, virtual, cloud, and hybrid solutions. The industry leader in email security solutions, Cisco delivers:
Fast, comprehensive email protection that can block spam and threats before they even hit your network
Flexible cloud, virtual, and physical deployment options to meet your ever-changing business needs
Outbound message control through on-device data-loss prevention (DLP), email encryption, and optional integration with the RSA enterprise DLP solution
One of the lowest total cost of ownership (TCO) email security solutions available
QUESTION 2
Which two characteristics represent a blended threat? (Choose two.)
A. man-in-the-middle attack
B. trojan horse attack
C. pharming attack
D. denial of service attack
E. day zero attack
Correct Answer: BE Explanation
Explanation/Reference:
Explanation: http://www.cisco.com/web/IN/about/network/threat_defense.html
Rogue developers create such threats by using worms, viruses, or application-embedded attacks. Botnets can be used to seed an attack, for example, rogue developers can use worms or application-embedded attacks, that is an attack that is hidden within application traffic such as web traffic or peer-to-peer shared files, to deposit “Trojans”. This combination of attack techniques – a virus or worm used to deposit a Trojan, for example-is relatively new and is known as a blended attack. A blended attack can also occur in phases: an initial attack of a virus with a Trojan that might open up an unsecured port on a computer, disable an access control list (ACL), or disarm antivirus software, with the goal of a more devastating attack to follow soon after. Host Firewall on servers and desktops/ laptops, day zero protection & intelligent behavioral based protection from application vulnerability and related flaws (within or inserted by virus, worms or Trojans) provided great level of confidence on what is happening within an organization on a normal day and when there is a attack situation, which segment and what has gone wrong and gives flexibility and control to stop such situations by having linkages of such devices with monitoring, log-analysis and event co-relation system.
» Read more about: Cisco 640-554 Cert Exam, Most Popular Cisco 640-554 Dump UP To 50% Off »
Categories
2025 Microsoft Top 20 Certification Materials
- Microsoft Azure Administrator –> az-104 dumps
- Microsoft Azure Fundamentals –> az-900 dumps
- Data Engineering on Microsoft Azure –> dp-203 dumps
- Developing Solutions for Microsoft Azure –> az-204 dumps
- Microsoft Power Platform Developer –> pl-400 dumps
- Designing and Implementing a Microsoft Azure AI Solution –> ai-102 dumps
- Microsoft Power BI Data Analyst –> pl-300 dumps
- Designing and Implementing Microsoft DevOps Solutions –> az-400 dumps
- Microsoft Azure Security Technologies –> az-500 dumps
- Microsoft Cybersecurity Architect –> sc-100 dumps
- Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM) –> mb-910 dumps
- Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP) –> mb-920 dumps
- Microsoft Azure Data Fundamentals –> dp-900 dumps
- Microsoft 365 Fundamentals –> ms-900 dumps
- Microsoft Security Compliance and Identity Fundamentals –> sc-900 dumps
- Microsoft Azure AI Fundamentals –> ai-900 dumps
- Microsoft Dynamics 365: Finance and Operations Apps Solution Architect –> mb-700 dumps
- Microsoft 365 Certified: Enterprise Administrator Expert –> ms-102 dumps
- Microsoft 365 Certified: Collaboration Communications Systems Engineer Associate –> ms-721 dumps
- Endpoint Administrator Associate –> md-102 dumps

