Cisco Certification Exam Prep Materials
Cisco CCNA Exam Prep Material Download
Cisco CCT Exam Prep Material Download
- Cisco 010-151 Dumps PDF
- Cisco 100-490 Dumps PDF
- Cisco 100-890 Dumps PDF
- Tips: Beginning February 10, the CCT Certification 500-150 FLDTEC v1.0 exam will replace the 100-490, 010-151, and 100-890 exams.
Cisco CyberOps Exam Prep Material Download
Cisco DevNet Exam Prep Material Download
Cisco CCNP Exam Prep Material Download
- Cisco 300-410 Dumps PDF
- Cisco 300-415 Dumps PDF
- Cisco 300-420 Dumps PDF
- Cisco 300-425 Dumps PDF
- Cisco 300-430 Dumps PDF
- Cisco 300-435 Dumps PDF
- Cisco 300-440 Dumps PDF
- Cisco 300-510 Dumps PDF
- Cisco 300-515 Dumps PDF
- Cisco 300-535 Dumps PDF
- Cisco 300-610 Dumps PDF
- Cisco 300-615 Dumps PDF
- Cisco 300-620 Dumps PDF
- Cisco 300-630 Dumps PDF
- Cisco 300-635 Dumps PDF
- Cisco 300-710 Dumps PDF
- Cisco 300-715 Dumps PDF
- Cisco 300-720 Dumps PDF
- Cisco 300-725 Dumps PDF
- Cisco 300-730 Dumps PDF
- Cisco 300-735 Dumps PDF
- Cisco 300-810 Dumps PDF
- Cisco 300-815 Dumps PDF
- Cisco 300-820 Dumps PDF
- Cisco 300-835 Dumps PDF
Cisco CCIE Exam Prep Material Download
- Cisco 350-401 Dumps PDF
- Cisco 350-501 Dumps PDF
- Cisco 350-601 Dumps PDF
- Cisco 350-701 Dumps PDF
- Cisco 350-801 Dumps PDF
Cisco CCDE Exam Prep Material Download
Cisco Other Exam Prep Material Download
- Cisco 500-052 Dumps PDF
- Cisco 500-210 Dumps PDF
- Cisco 500-220 Dumps PDF
- Cisco 500-420 Dumps PDF
- Cisco 500-442 Dumps PDF
- Cisco 500-444 Dumps PDF
- Cisco 500-470 Dumps PDF
- Cisco 500-490 Dumps PDF
- Cisco 500-560 Dumps PDF
- Cisco 500-710 Dumps PDF
- Cisco 700-150 Dumps PDF
- Cisco 700-750 Dumps PDF
- Cisco 700-760 Dumps PDF
- Cisco 700-765 Dumps PDF
- Cisco 700-805 Dumps PDF
- Cisco 700-821 Dumps PDF
- Cisco 700-826 Dumps PDF
- Cisco 700-846 Dumps PDF
- Cisco 700-905 Dumps PDF
- Cisco 820-605 Dumps PDF
Fortinet Exam Dumps
fortinet nse4_fgt-6.4 dumps (pdf + vce)
fortinet nse4_fgt-6.2 dumps (pdf + vce)
fortinet nse5_faz-6.4 dumps (pdf + vce)
fortinet nse5_faz-6.2 dumps (pdf + vce)
fortinet nse5_fct-6.2 dumps (pdf + vce)
fortinet nse5_fmg-6.4 dumps (pdf + vce)
fortinet nse5_fmg-6.2 dumps (pdf + vce)
fortinet nse6_fml-6.2 dumps (pdf + vce)
fortinet nse6_fnc-8.5 dumps (pdf + vce)
fortinet nse7_efw-6.4 dumps (pdf + vce)
fortinet nse7_efw-6.2 dumps (pdf + vce)
fortinet nse7_sac-6.2 dumps (pdf + vce)
fortinet nse7_sdw-6.4 dumps (pdf + vce)
fortinet nse8_811 dumps (pdf + vce)

It’s definitely worth it. First, you should understand Pass4itSure. This is a website that specializes in providing the latest updates to IT certification exam practice materials. Has helped many customers succeed and experience. To pass the Cisco 300-410 exam, click https://www.pass4itsure.com/300-410.html for the latest Cisco 300-410 dumps (PDF and VCE). Guaranteed to help you successfully pass the exam!
Pass4itSure free sharing part of Cisco 300-410 exam dumps (PDF + online)
What is the best way to prepare for the Cisco 300-410 exam?
I can share how I do, which is the same method for everyone. Pass4itSure Cisco 300-410 dumps!
Cisco 300-410 exam dumps PDF
| Cisco 300-410 dumps PDF | From Drive |
| https://drive.google.com/file/d/10qiSzrt2tedmDF4vSfMpjujMNJn9YEEs/view?usp=sharing |
Cisco 300-410 online practice test
Following are some new 300–410 exam questions:
QUESTION 1
Which statement about IPv6 ND inspection is true?
A. It learns and secures bindings for stateless autoconfiguration addresses in Layer 3 neighbor tables.
B. It learns and secures bindings for stateless autoconfiguration addresses in Layer 2 neighbor tables.
C. It learns and secures bindings for stateful autoconfiguration addresses in Layer 3 neighbor tables.
D. It learns and secures bindings for stateful autoconfiguration addresses in Layer 2 neighbor tables.
Correct Answer: B
IPv6 ND inspection learns and secures bindings for stateless autoconfiguration addresses in Layer 2 neighbor tables.
IPv6 ND inspection analyzes neighbor discovery messages in order to build a trusted binding table database and IPv6
neighbor discovery messages that do not have valid bindings are dropped. A neighbor discovery message is considered
trustworthy if its IPv6-to-MAC mapping is verifiable.
This feature mitigates some of the inherent vulnerabilities for the neighbor discovery mechanism, such as attacks on
duplicate address detection (DAD), address resolution, device discovery, and the neighbor cache.
Reference: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipv6_fhsec/configuration/15-s/ip6f-15-sbook/ip6-snooping.pdf
QUESTION 2
A network engineer is configuring a DHCP server to support a specialized application. Which additional DHCP feature
must be enabled to support the delivery of various additional parameters to DHCP clients?
A. modules
B. vendor extensions
C. options
D. Scopes
Correct Answer: C
QUESTION 3
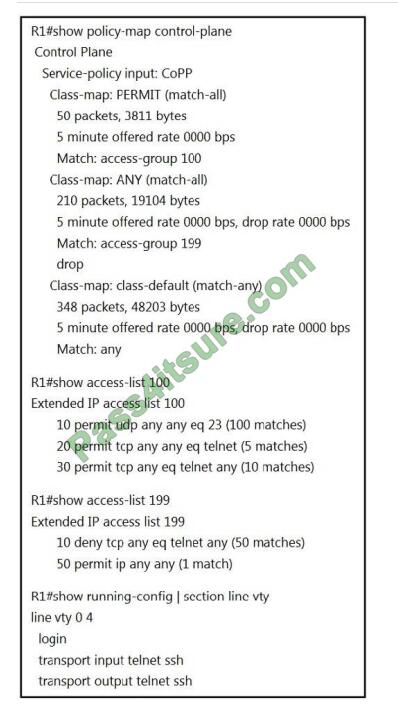
Refer to the exhibit. Which two actions restrict access to router R1 by SSH? (Choose two.)
A. Remove class-map ANY from service-policy CoPP.
B. Configure transport output ssh on line vty and remove sequence 20 from access-list 100.
C. Configure transport input ssh on line vty and remove sequence 30 from access-list 100.
D. Remove sequence 10 from access-list 100 and add sequence 20 deny tcp any any eq telnet to access-list 199.
E. Configure transport output ssh on line vty and remove sequence 10 from access-list 199.
Correct Answer: BC
To only allow SSH to R1, we have to: + Deny Telnet in ACL 100 because the action of class-map: PERMIT is “permit” +
Permit Telnet in ACL 199 because the action of class-map: ANY is “drop” But:
+
In ACL 100 there is a permit statement for Telnet traffic “20 permit TCP any eq telnet (5 matches)” which is not
correct so we must remove this statement.
+
In ACL 199 there is an ACL statement “10 deny tcp any eq telnet any (50 matches)”. This statement is aimed at Telnet
traffic leaving R1 which is not correct so we must remove this statement. Note:
+
The command “transport output telnet ssh” allows telnet and SSH from this device (to other devices).
+
Telnet is TCP port 23. + When using Telnet on the source port, it affects Telnet traffic leaving from R1.\
QUESTION 4
Users were moved from the local DHCP server to the remote corporate DHCP server. After the move, none of the users
were able to use the network. Which two issues will prevent this setup from working properly? (Choose two)
A. Auto-QoS is blocking DHCP traffic.
B. The DHCP server IP address configuration is missing locally
C. 802.1X is blocking DHCP traffic
D. The broadcast domain is too large for proper DHCP propagation
E. The route to the new DHCP server is missing
Correct Answer: BE
QUESTION 5
Refer to the exhibit.
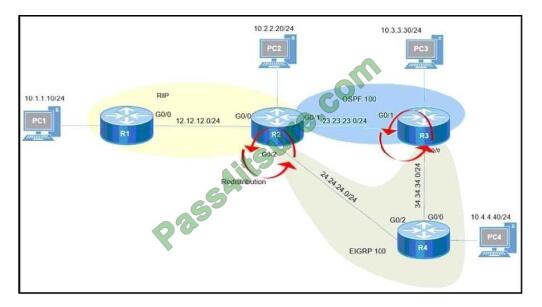
Redistribution is enabled between the routing protocols, and nowPC2 PC3 and PC4 cannot reach PC1. What are the
two solutions to fix the problem? (Choose two.)
A. Filter RIP routes back into RIP when redistributing into RIP in R2
B. Filter OSPF routes into RIP from EIGRP when redistributing into RIP in R2
C. Filter all routes except RIP routes when redistributing into EIGRP in R2.
D. Filter RIP AND OSPF routes back into OSPF from EIGRP when redistributing into OSPF in R2
E. Filter all routes except EIGRP routes when redistributing into OSPF in R3.
Correct Answer: AB
Even PC2 cannot reach PC1 so there is something wrong with RIP redistribution in R2. Because RIP has a higher
Administrative Distance (AD) value than OSPF and EIGRP so it will be looped when doing mutual redistribution.
QUESTION 6
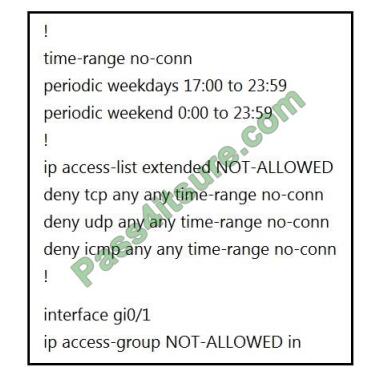
Refer to the exhibit. A network administrator wants to block all traffic toward the Internet after business hours and on
weekends. When the administrator applies an access list on interface Gi0/1, all traffic is blocked and there is no access
to the Internet at any time.
Which action resolves the issue?
A. Add the permitted IP any time-range no-conn statement after the deny udp any time-range no-conn command in
the access list.
B. Add the permitted IP any statement after the deny ICMP any time-range no-conn command in the access list.
C. Add the permit allowed time-range no-conn statement after the deny ICMP any time-range no-conn command in
the access list.
D. Add the permitted IP any time-range no-conn statement after the deny ICMP any time-range no-conn command
in the access list.
Correct Answer: B
QUESTION 7
Which security feature can protect DMVPN tunnels?
A. IPsec
B. TACACS+
C. RTBH
D. RADIUS
Correct Answer: A
QUESTION 8
Refer to the exhibit.
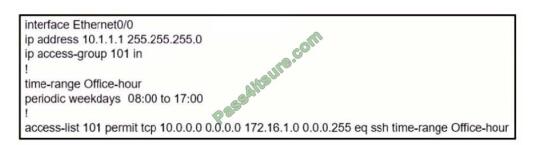
An IT staff member comes into the office during normal office hours and cannot access devices through SSH Which
action should be taken to resolve this issue?
A. Modify the access list to use the correct IP address.
B. Configure the correct time range.
C. Modify the access list to correct the subnet mask
D. Configure the access list in the outbound direction.
Correct Answer: A
To ACL should be permitted TCP 101 10.1.1.1 0.0.0.0
QUESTION 9
Which two statements about redistributing EIGRP into OSPF are true? (Choose two)
A. The redistributed EIGRP routes appear as type 3 LSAs in the OSPF database
B. The redistributed EIGRP routes appear as type 5 LSAs in the OSPF database
C. The administrative distance of the redistributed routes is 170
D. The redistributed EIGRP routes appear as OSPF external type 1
E. The redistributed EIGRP routes as placed into an OSPF area whose area ID matches the EIGRP autonomous
system number
F. The redistributed EIGRP routes appear as OSPF external type 2 routes in the routing table
Correct Answer: BF
QUESTION 10
Which two components are needed for a service provider to utilize the LVPN MPLS application? (Choose two.)
A. The P routers must be configured for MP-iBGP toward the PE routers
B. The P routers must be configured with RSVP.
C. The PE routers must be configured for MP-iBGP with other PE routers
D. The PE routers must be configured for MP-eBGP to connect to CEs
E. The P and PE routers must be configured with LDP or RSVP
Correct Answer: AD
QUESTION 11
A network administrator is troubleshooting a redistribution of OSPF routes into EIGRP.
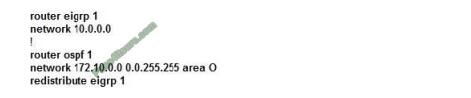
Given the exhibited commands, which statement is true?
A. Redistributed routes will have an external type of 1 and a metric of 1.
B. Redistributed routes will have an external type of 2 and a metric of 20.
C. Redistributed routes will maintain their original OSPF routing metric.
D. Redistributed routes will have a default metric of 0 and will be treated as reachable and advertised.
E. Redistributed routes will have a default metric of 0 but will be treated as unreachable and not advertised.
Correct Answer: B
By default, all routes redistributed into OSPF will be tagged as external type 2 (E2) with a metric of 20, except for BGP
routes (with a metric of 1).
Note:
The cost of a type 2 route is always the external cost, irrespective of the interior cost to reach that route. A type 1 cost is
the addition of the external cost and the internal cost used to reach that route.
QUESTION 12

Refer to the exhibit. A network administrator is troubleshooting the OSPF adjacency issue by going through the console logs in the router, but due to an overwhelming log messages stream, it is impossible to capture the problem. Which two commands reduce console log messages to relevant OSPF neighbor problem details so that the issue can be resolved?
(Choose two.)
A. debug condition OSPF neighbor
B. debug condition interface
C. debug condition session-id ADJCHG
D. debug condition all
Correct Answer: AB
QUESTION 13
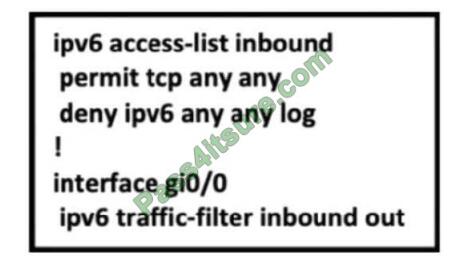
Refer to the exhibit. A network administrator configured an IPv6 access list to allow TCP return traffic only, but it is not
working as expected. Which changes resolve this issue?
A. ipv6 access-list inbound permit TCP any syn deny ipv6 any log! interface gi0/0 ipv6 traffic-filter inbound out
B. ipv6 access-list inbound permit TCP any syn deny ipv6 any log! interface gi0/0 ipv6 traffic-filter inbound in
C. ipv6 access-list inbound permit TCP any established deny ipv6 any log! interface gi0/0 ipv6 traffic-filter
inbound in
D. ipv6 access-list inbound permit TCP any established deny ipv6 any log! Questions and Answers PDF P-133
interface gi0/0 ipv6 traffic-filter inbound out
Correct Answer: C
QUESTION 14
Which method changes the forwarding decision that a router makes without first changing the routing table or
influencing the IP data plane?
A. nonbroadcast multiaccess
B. packet switching
C. policy-based routing
D. forwarding information base
Correct Answer: C
QUESTION 15
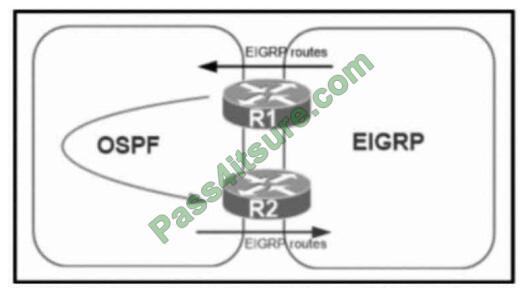
Refer to the exhibit. A network administrator configured mutual redistribution on R1 and R2 routers, which caused
instability in the network. Which action resolves the issue?
A. Set a tag in the route map when redistributing EIGRP into OSPF on R1. and match the same tag on R2 to deny when
redistributing OSPF into EIGRP.
B. Set a tag in the route map when redistributing EIGRP into OSPF on R1. and match the same tag on R2 to allow
when redistributing OSPF into EIGRP.
C. Advertise summary routes of EIGRP to OSPF and deny specific EIGRP routes when redistributing into OSPF.
D. Apply a prefix-list of EIGRP network routes in the OSPF domain on R1 to propagate back into the EIGRP routing
domain.
Correct Answer: A
More new 300–410 exam questions: Pass4itSure.
2021 latest 300–410 pdf: https://drive.google.com/file/d/10qiSzrt2tedmDF4vSfMpjujMNJn9YEEs/view?usp=sharing
Finally:
Pass4itSure Cisco 300-410 dumps is your right choice. It contains the latest 300-410 exam questions and answers to help you pass the exam easily. One step ahead of others. You can access Pas4itSure for the full 300–410 exam dumps https://www.pass4itsure.com/300-410.html (two learning modes are available: PDF and VCE). Study hard and wish you success.
Related
Discover more from Exampass: Collection of Cisco (CCNA, CCNP, Meraki Solutions Specialist, CCDP...) exam questions and answers from Pass4itsure
Subscribe to get the latest posts sent to your email.
Written by Ralph K. Merritt
We are here to help you study for Cisco certification exams. We know that the Cisco series (CCNP, CCDE, CCIE, CCNA, DevNet, Special and other certification exams are becoming more and more popular, and many people need them. In this era full of challenges and opportunities, we are committed to providing candidates with the most comprehensive and comprehensive Accurate exam preparation resources help them successfully pass the exam and realize their career dreams. The Exampass blog we established is based on the Pass4itsure Cisco exam dump platform and is dedicated to collecting the latest exam resources and conducting detailed classification. We know that the most troublesome thing for candidates during the preparation process is often the massive amount of learning materials and information screening. Therefore, we have prepared the most valuable preparation materials for candidates to help them prepare more efficiently. With our rich experience and deep accumulation in Cisco certification, we provide you with the latest PDF information and the latest exam questions. These materials not only include the key points and difficulties of the exam, but are also equipped with detailed analysis and question-answering techniques, allowing candidates to deeply understand the exam content and master how to answer questions. Our ultimate goal is to help you study for various Cisco certification exams, so that you can avoid detours in the preparation process and get twice the result with half the effort. We believe that through our efforts and professional guidance, you will be able to easily cope with exam challenges, achieve excellent results, and achieve both personal and professional improvement. In your future career, you will be more competitive and have broader development space because of your Cisco certification.
Categories
2025 Microsoft Top 20 Certification Materials
- Microsoft Azure Administrator –> az-104 dumps
- Microsoft Azure Fundamentals –> az-900 dumps
- Data Engineering on Microsoft Azure –> dp-203 dumps
- Developing Solutions for Microsoft Azure –> az-204 dumps
- Microsoft Power Platform Developer –> pl-400 dumps
- Designing and Implementing a Microsoft Azure AI Solution –> ai-102 dumps
- Microsoft Power BI Data Analyst –> pl-300 dumps
- Designing and Implementing Microsoft DevOps Solutions –> az-400 dumps
- Microsoft Azure Security Technologies –> az-500 dumps
- Microsoft Cybersecurity Architect –> sc-100 dumps
- Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM) –> mb-910 dumps
- Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP) –> mb-920 dumps
- Microsoft Azure Data Fundamentals –> dp-900 dumps
- Microsoft 365 Fundamentals –> ms-900 dumps
- Microsoft Security Compliance and Identity Fundamentals –> sc-900 dumps
- Microsoft Azure AI Fundamentals –> ai-900 dumps
- Microsoft Dynamics 365: Finance and Operations Apps Solution Architect –> mb-700 dumps
- Microsoft 365 Certified: Enterprise Administrator Expert –> ms-102 dumps
- Microsoft 365 Certified: Collaboration Communications Systems Engineer Associate –> ms-721 dumps
- Endpoint Administrator Associate –> md-102 dumps

