Cisco Certification Exam Prep Materials
Cisco CCNA Exam Prep Material Download
Cisco CCT Exam Prep Material Download
- Cisco 010-151 Dumps PDF
- Cisco 100-490 Dumps PDF
- Cisco 100-890 Dumps PDF
- Tips: Beginning February 10, the CCT Certification 500-150 FLDTEC v1.0 exam will replace the 100-490, 010-151, and 100-890 exams.
Cisco CyberOps Exam Prep Material Download
Cisco DevNet Exam Prep Material Download
Cisco CCNP Exam Prep Material Download
- Cisco 300-410 Dumps PDF
- Cisco 300-415 Dumps PDF
- Cisco 300-420 Dumps PDF
- Cisco 300-425 Dumps PDF
- Cisco 300-430 Dumps PDF
- Cisco 300-435 Dumps PDF
- Cisco 300-440 Dumps PDF
- Cisco 300-510 Dumps PDF
- Cisco 300-515 Dumps PDF
- Cisco 300-535 Dumps PDF
- Cisco 300-610 Dumps PDF
- Cisco 300-615 Dumps PDF
- Cisco 300-620 Dumps PDF
- Cisco 300-630 Dumps PDF
- Cisco 300-635 Dumps PDF
- Cisco 300-710 Dumps PDF
- Cisco 300-715 Dumps PDF
- Cisco 300-720 Dumps PDF
- Cisco 300-725 Dumps PDF
- Cisco 300-730 Dumps PDF
- Cisco 300-735 Dumps PDF
- Cisco 300-810 Dumps PDF
- Cisco 300-815 Dumps PDF
- Cisco 300-820 Dumps PDF
- Cisco 300-835 Dumps PDF
Cisco CCIE Exam Prep Material Download
- Cisco 350-401 Dumps PDF
- Cisco 350-501 Dumps PDF
- Cisco 350-601 Dumps PDF
- Cisco 350-701 Dumps PDF
- Cisco 350-801 Dumps PDF
Cisco CCDE Exam Prep Material Download
Cisco Other Exam Prep Material Download
- Cisco 500-052 Dumps PDF
- Cisco 500-210 Dumps PDF
- Cisco 500-220 Dumps PDF
- Cisco 500-420 Dumps PDF
- Cisco 500-442 Dumps PDF
- Cisco 500-444 Dumps PDF
- Cisco 500-470 Dumps PDF
- Cisco 500-490 Dumps PDF
- Cisco 500-560 Dumps PDF
- Cisco 500-710 Dumps PDF
- Cisco 700-150 Dumps PDF
- Cisco 700-750 Dumps PDF
- Cisco 700-760 Dumps PDF
- Cisco 700-765 Dumps PDF
- Cisco 700-805 Dumps PDF
- Cisco 700-821 Dumps PDF
- Cisco 700-826 Dumps PDF
- Cisco 700-846 Dumps PDF
- Cisco 700-905 Dumps PDF
- Cisco 820-605 Dumps PDF
Fortinet Exam Dumps
fortinet nse4_fgt-6.4 dumps (pdf + vce)
fortinet nse4_fgt-6.2 dumps (pdf + vce)
fortinet nse5_faz-6.4 dumps (pdf + vce)
fortinet nse5_faz-6.2 dumps (pdf + vce)
fortinet nse5_fct-6.2 dumps (pdf + vce)
fortinet nse5_fmg-6.4 dumps (pdf + vce)
fortinet nse5_fmg-6.2 dumps (pdf + vce)
fortinet nse6_fml-6.2 dumps (pdf + vce)
fortinet nse6_fnc-8.5 dumps (pdf + vce)
fortinet nse7_efw-6.4 dumps (pdf + vce)
fortinet nse7_efw-6.2 dumps (pdf + vce)
fortinet nse7_sac-6.2 dumps (pdf + vce)
fortinet nse7_sdw-6.4 dumps (pdf + vce)
fortinet nse8_811 dumps (pdf + vce)
Valid CompTIA CS0-002 dumps questions shared by Pass4itsure for helping to pass the CompTIA CS0-002 exam! Get the newest Pass4itsure CS0-002 exam dumps with VCE and PDF here: https://www.pass4itsure.com/cs0-002.html (416 Q&As Dumps).
Suitable for CS0-002 complete CompTIA learning pathway
The content is rich and diverse, and learning will not become boring. You can learn in multiple ways through the CompTIA CS0-002 exam.
- Download
- Watch the video
- Answer practice questions, the actual test
CompTIA Cybersecurity Analyst (CySA+) CS0-002 Exam
Free CompTIA CS0-002 dumps download
[PDF] Free CompTIA CS0-002 dumps download https://drive.google.com/file/d/13B6BXoYMDmvR9lXyXbSBk80iw92m2szu/view?usp=sharing
Pass4itsure offers the latest CompTIA CS0-002 practice test free of charge 1-13
QUESTION 1
A development team uses open-source software and follows an Agile methodology with two-week sprints. Last month,
the security team filed a bug for an insecure version of a common library. The DevOps team updated the library on the
server, and then the security team rescanned the server to verify it was no longer vulnerable. This month, the security
team found the same vulnerability on the server.
Which of the following should be done to correct the cause of the vulnerability?
A. Deploy a WAF in front of the application.
B. Implement a software repository management tool.
C. Install a HIPS on the server.
D. Instruct the developers to use input validation in the code.
Correct Answer: B
QUESTION 2
An employee in the billing department accidentally sent a spreadsheet containing payment card data to a recipient
outside the organization The employee intended to send the spreadsheet to an internal staff member with a similar
name and was unaware of the mistake until the recipient replied to the message In addition to retraining the employee,
which of the following would prevent this from happening in the future?
A. Implement outgoing filter rules to quarantine messages that contain card data
B. Configure the outgoing mail filter to allow attachments only to addresses on the whitelist
C. Remove all external recipients from the employee\\’s address book
D. Set the outgoing mail filter to strip spreadsheet attachments from all messages.
Correct Answer: B
QUESTION 3
During routine monitoring, a security analyst discovers several suspicious websites that are communicating with a local
host. The analyst queries for IP 192.168.50.2 for a 24-hour period:

To further investigate, the analyst should request PCAP for SRC 192.168.50.2 and __________.
A. DST 138.10.2.5.
B. DST 138.10.25.5.
C. DST 172.10.3.5.
D. DST 172.10.45.5.
E. DST 175.35.20.5.
Correct Answer: C
QUESTION 4
Which of the following technologies can be used to house the entropy keys for disk encryption on desktops and
laptops?
A. Self-encrypting drive
B. Bus encryption
C. TPM
D. HSM
Correct Answer: A
QUESTION 5
A web developer wants to create a new web part within the company website that aggregates sales from individual team
sites. A cybersecurity analyst wants to ensure security measurements are implemented during this process. Which of
the following remediation actions should the analyst take to implement a vulnerability management process?
A. Personnel training
B. Vulnerability scan
C. Change management
D. Sandboxing
Correct Answer: C
QUESTION 6
Which of the following is the use of tools to simulate the ability for an attacker to gain access to a specified network?
A. Reverse engineering
B. Fuzzing
C. Penetration testing
D. Network mapping
Correct Answer: C
QUESTION 7
A Chief Information Security Officer (CISO) is concerned the development team, which consists of contractors, has too
much access to customer data. Developers use personal workstations, giving the company little to no visibility into the
development activities.
Which of the following would be BEST to implement to alleviate the CISO\\’s concern?
A. DLP
B. Encryption
C. Test data
D. NDA
Correct Answer: A
QUESTION 8
A security analyst conducted a risk assessment on an organization\\’s wireless network and identified a high-risk
element in the implementation of data confidentially protection. Which of the following is the BEST technical security
control to mitigate this risk?
A. Switch to RADIUS technology
B. Switch to TACACS+ technology.
C. Switch to 802 IX technology
D. Switch to the WPA2 protocol.
Correct Answer: B
QUESTION 9
Which of the following should be found within an organization\\’s acceptable use policy?
A. Passwords must be eight characters in length and contain at least one special character.
B. Customer data must be handled properly, stored on company servers, and encrypted when possible
C. Administrator accounts must be audited monthly, and inactive accounts should be removed.
D. Consequences of violating the policy could include discipline up to and including termination.
Correct Answer: D
QUESTION 10
Bootloader malware was recently discovered on several company workstations. All the workstations run Windows and
are current models with UEFI capability. Which of the following UEFI settings is the MOST likely cause of the
infections?
A. Compatibility mode
B. Secure boot mode
C. Native mode
D. Fast boot mode
Correct Answer: A
QUESTION 11
A security analyst is responding to an incident on a web server on the company network that is making a large number
of outbound requests over DNS Which of the following is the FIRST step the analyst should take to evaluate this
potential indicator of compromise\\’?
A. Run an anti-malware scan on the system to detect and eradicate the current threat
B. Start a network capture on the system to look into the DNS requests to validate command and control traffic.
C. Shut down the system to prevent further degradation of the company network
D. Reimage the machine to remove the threat completely and get back to a normal running state.
E. Isolate the system on the network to ensure it cannot access other systems while evaluation is underway.
Correct Answer: A
QUESTION 12
A security analyst is reviewing the logs from an internal chat server. The chat.log file is too large to review manually, so
the analyst wants to create a shorter log file that only includes lines associated with a user demonstrating anomalous
activity. Below is a snippet of the log:

Which of the following commands would work BEST to achieve the desired result?
A. grep -v chatter14 chat.log
B. grep -i pythonfun chat.log
C. grep -i javashark chat.log
D. grep -v javashark chat.log
E. grep -v pythonfun chat.log
F. grep -i chatter14 chat.log
Correct Answer: D
QUESTION 13
During an investigation, a security analyst identified machines that are infected with malware the antivirus was unable to
detect. Which of the following is the BEST place to acquire evidence to perform data carving?
A. The system memory
B. The hard drive
C. Network packets
D. The Windows Registry
Correct Answer: A
Reference: https://resources.infosecinstitute.com/memory-forensics/#gref https://www.computerhope.com/jargon/d/datacarving.htm
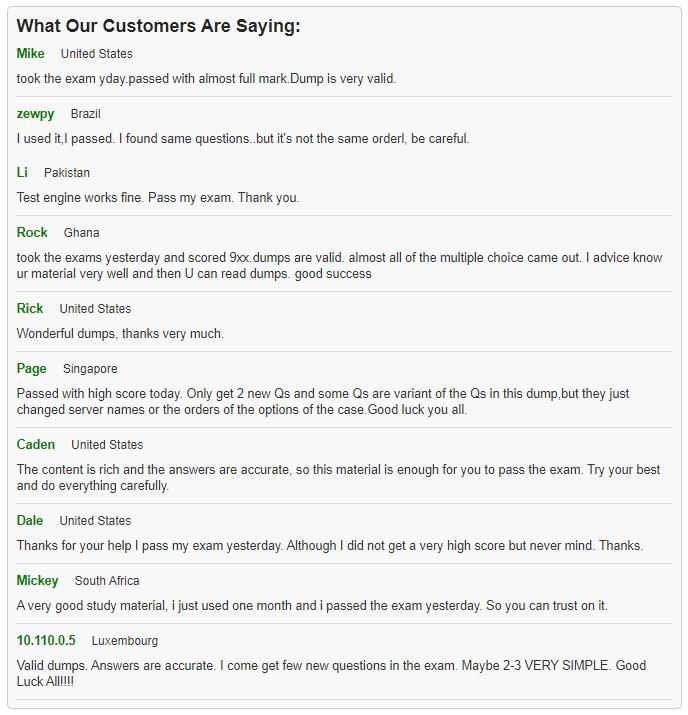
What customers say about Pass4itsure
Latest discount code “2020PASS” – Pass4itsure
Summarize:
[Q1-Q13] Free CompTIA CS0-002 dumps pdf download https://drive.google.com/file/d/13B6BXoYMDmvR9lXyXbSBk80iw92m2szu/view?usp=sharing
Share all the resources: Latest CompTIA CS0-002 practice questions, latest CompTIA CS0-002 pdf dumps, CompTIA CS0-002 exam video learning. Latest update CompTIA CS0-002 dumps https://www.pass4itsure.com/cs0-002.html Study hard and practices a lot. This will help you prepare for the CS0-002 exam. Good luck!
Related
Discover more from Exampass: Collection of Cisco (CCNA, CCNP, Meraki Solutions Specialist, CCDP...) exam questions and answers from Pass4itsure
Subscribe to get the latest posts sent to your email.
Written by Ralph K. Merritt
We are here to help you study for Cisco certification exams. We know that the Cisco series (CCNP, CCDE, CCIE, CCNA, DevNet, Special and other certification exams are becoming more and more popular, and many people need them. In this era full of challenges and opportunities, we are committed to providing candidates with the most comprehensive and comprehensive Accurate exam preparation resources help them successfully pass the exam and realize their career dreams. The Exampass blog we established is based on the Pass4itsure Cisco exam dump platform and is dedicated to collecting the latest exam resources and conducting detailed classification. We know that the most troublesome thing for candidates during the preparation process is often the massive amount of learning materials and information screening. Therefore, we have prepared the most valuable preparation materials for candidates to help them prepare more efficiently. With our rich experience and deep accumulation in Cisco certification, we provide you with the latest PDF information and the latest exam questions. These materials not only include the key points and difficulties of the exam, but are also equipped with detailed analysis and question-answering techniques, allowing candidates to deeply understand the exam content and master how to answer questions. Our ultimate goal is to help you study for various Cisco certification exams, so that you can avoid detours in the preparation process and get twice the result with half the effort. We believe that through our efforts and professional guidance, you will be able to easily cope with exam challenges, achieve excellent results, and achieve both personal and professional improvement. In your future career, you will be more competitive and have broader development space because of your Cisco certification.
Categories
2025 Microsoft Top 20 Certification Materials
- Microsoft Azure Administrator –> az-104 dumps
- Microsoft Azure Fundamentals –> az-900 dumps
- Data Engineering on Microsoft Azure –> dp-203 dumps
- Developing Solutions for Microsoft Azure –> az-204 dumps
- Microsoft Power Platform Developer –> pl-400 dumps
- Designing and Implementing a Microsoft Azure AI Solution –> ai-102 dumps
- Microsoft Power BI Data Analyst –> pl-300 dumps
- Designing and Implementing Microsoft DevOps Solutions –> az-400 dumps
- Microsoft Azure Security Technologies –> az-500 dumps
- Microsoft Cybersecurity Architect –> sc-100 dumps
- Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM) –> mb-910 dumps
- Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP) –> mb-920 dumps
- Microsoft Azure Data Fundamentals –> dp-900 dumps
- Microsoft 365 Fundamentals –> ms-900 dumps
- Microsoft Security Compliance and Identity Fundamentals –> sc-900 dumps
- Microsoft Azure AI Fundamentals –> ai-900 dumps
- Microsoft Dynamics 365: Finance and Operations Apps Solution Architect –> mb-700 dumps
- Microsoft 365 Certified: Enterprise Administrator Expert –> ms-102 dumps
- Microsoft 365 Certified: Collaboration Communications Systems Engineer Associate –> ms-721 dumps
- Endpoint Administrator Associate –> md-102 dumps

