Cisco Certification Exam Prep Materials
Cisco CCNA Exam Prep Material Download
Cisco CCT Exam Prep Material Download
- Cisco 010-151 Dumps PDF
- Cisco 100-490 Dumps PDF
- Cisco 100-890 Dumps PDF
- Tips: Beginning February 10, the CCT Certification 500-150 FLDTEC v1.0 exam will replace the 100-490, 010-151, and 100-890 exams.
Cisco CyberOps Exam Prep Material Download
Cisco DevNet Exam Prep Material Download
Cisco CCNP Exam Prep Material Download
- Cisco 300-410 Dumps PDF
- Cisco 300-415 Dumps PDF
- Cisco 300-420 Dumps PDF
- Cisco 300-425 Dumps PDF
- Cisco 300-430 Dumps PDF
- Cisco 300-435 Dumps PDF
- Cisco 300-440 Dumps PDF
- Cisco 300-510 Dumps PDF
- Cisco 300-515 Dumps PDF
- Cisco 300-535 Dumps PDF
- Cisco 300-610 Dumps PDF
- Cisco 300-615 Dumps PDF
- Cisco 300-620 Dumps PDF
- Cisco 300-630 Dumps PDF
- Cisco 300-635 Dumps PDF
- Cisco 300-710 Dumps PDF
- Cisco 300-715 Dumps PDF
- Cisco 300-720 Dumps PDF
- Cisco 300-725 Dumps PDF
- Cisco 300-730 Dumps PDF
- Cisco 300-735 Dumps PDF
- Cisco 300-810 Dumps PDF
- Cisco 300-815 Dumps PDF
- Cisco 300-820 Dumps PDF
- Cisco 300-835 Dumps PDF
Cisco CCIE Exam Prep Material Download
- Cisco 350-401 Dumps PDF
- Cisco 350-501 Dumps PDF
- Cisco 350-601 Dumps PDF
- Cisco 350-701 Dumps PDF
- Cisco 350-801 Dumps PDF
Cisco CCDE Exam Prep Material Download
Cisco Other Exam Prep Material Download
- Cisco 500-052 Dumps PDF
- Cisco 500-210 Dumps PDF
- Cisco 500-220 Dumps PDF
- Cisco 500-420 Dumps PDF
- Cisco 500-442 Dumps PDF
- Cisco 500-444 Dumps PDF
- Cisco 500-470 Dumps PDF
- Cisco 500-490 Dumps PDF
- Cisco 500-560 Dumps PDF
- Cisco 500-710 Dumps PDF
- Cisco 700-150 Dumps PDF
- Cisco 700-750 Dumps PDF
- Cisco 700-760 Dumps PDF
- Cisco 700-765 Dumps PDF
- Cisco 700-805 Dumps PDF
- Cisco 700-821 Dumps PDF
- Cisco 700-826 Dumps PDF
- Cisco 700-846 Dumps PDF
- Cisco 700-905 Dumps PDF
- Cisco 820-605 Dumps PDF
Fortinet Exam Dumps
fortinet nse4_fgt-6.4 dumps (pdf + vce)
fortinet nse4_fgt-6.2 dumps (pdf + vce)
fortinet nse5_faz-6.4 dumps (pdf + vce)
fortinet nse5_faz-6.2 dumps (pdf + vce)
fortinet nse5_fct-6.2 dumps (pdf + vce)
fortinet nse5_fmg-6.4 dumps (pdf + vce)
fortinet nse5_fmg-6.2 dumps (pdf + vce)
fortinet nse6_fml-6.2 dumps (pdf + vce)
fortinet nse6_fnc-8.5 dumps (pdf + vce)
fortinet nse7_efw-6.4 dumps (pdf + vce)
fortinet nse7_efw-6.2 dumps (pdf + vce)
fortinet nse7_sac-6.2 dumps (pdf + vce)
fortinet nse7_sdw-6.4 dumps (pdf + vce)
fortinet nse8_811 dumps (pdf + vce)
Valid Cisco 700-765 questions shared by Pass4itsure for helping to pass the Cisco 700-765 exam! Get the newest Pass4itsure Cisco 700-765 exam dumps with VCE and PDF here: https://www.pass4itsure.com/700-765.html (92 Q&As Dumps).
[Free PDF] Cisco 700-765 pdf Q&As https://drive.google.com/file/d/1mW2LCS8B9EjxKfVJjXv7Hs2L9SWBSrkQ/view?usp=sharing
Suitable for 700-765 complete Cisco learning pathway
The content is rich and diverse, and learning will not become boring. You can learn in multiple ways through the Cisco 700-765 exam.
- Download
- Answer practice questions, the actual Cisco 700-765 test
Cisco 700-765 Cisco Security Architecture for System Engineers (ASASE)
Free Cisco 700-765 dumps download
[PDF] Free Cisco 700-765 dumps pdf download https://drive.google.com/file/d/1mW2LCS8B9EjxKfVJjXv7Hs2L9SWBSrkQ/view?usp=sharing
Pass4itsure offers the latest Cisco 700-765 practice test free of charge 1-13
QUESTION 1
Where do you start to achieve true network visibility?
A. Fabric Level
B. IT
C. OT
D. Branches
Correct Answer: A
QUESTION 2
How does AMP\\’s file reputation feature help customers?
A. It increases the protection to systems with exact fingerprinting
B. It increases the accuracy of threat detection with Big Data analytics
C. It enables point in time detection through a one-to-one engine
D. It enables secure web browsing with cognitive threat analytics
Correct Answer: B
QUESTION 3
Which feature of ISE provides role based access control and command level authorization with logging for auditing?
A. Context-aware access
B. Centralized policy management
C. Platform exchange grid
D. TACACS+ Device Administration
Correct Answer: D
QUESTION 4
In the Campus NGFW use case, which capability is provided by NGFW and NGIPS?
A. Flexible AAA Options
B. Identity Services Engine
C. Differentiated Mobile Access
D. High throughput maintained while still protecting domains against threats
Correct Answer: D
QUESTION 5
Which statement best embodies trust-centric security?
A. Protect users from attacks by enabling strict security policies.
B. Prevent attacks via an intelligence-based policy then detect, investigate, and remediate.
C. Verify before granting access via identity-based policies for users, devices, apps, and locations.
D. Verify before granting access via MDM software.
Correct Answer: C
QUESTION 6
Which Web Security feature allows employees to utilize web applications while also having the ability to bock or monitor
problematic applications?
A. Realtime Application Sandboxing
B. Application Phishing
C. Application Visibility and Control
D. Layered Scanning and Control
Correct Answer: C
QUESTION 7
Which three customer business objectives does Cisco\\’s Advanced Threat solutions address? (Choose Three)
A. Lower TCO through intelligent API management
B. Visibility and control with a managed environment
C. Accelerated firewall implementation
D. Complete protection with holistic defense
E. Comprehensive support with flexible solutions
F. Secure communications with advanced access
Correct Answer: BDE
QUESTION 8
What two areas present a security challenge for customers? (Choose Two)
A. OT environments
B. Email
C. Corporate printers
D. IT departments
E. loT devices
Correct Answer: BE
QUESTION 9
How does SD-WAN protect network traffic from end-to-end\\’?
A. Segmentation
B. Automation
C. Analyzation
D. Management
Correct Answer: A
QUESTION 10
What are three key benefits of Cisco NGFW? (Choose Three)
A. Reduces complexity
B. Reduces throughput
C. Increases traffic latency
D. identifies anomalous traffic
E. Prepares defenses
F. Detects and remediates threats faster
Correct Answer: AEF
QUESTION 11
Which feature of ISE has the capability to encounter a device new on the market and correctly profile it to onboard it
quickly and easily?
A. Context-aware access
B. Centralized policy management
C. Platform exchange grid
D. Device profiling
Correct Answer: D
QUESTION 12
What feature of web security filters websites based on who what where, how, and when to assign a website a score?
A. Sandbox Filtering
B. Reputation Filtering
C. Malware Filtering D. URL Analytics
Correct Answer: D
QUESTION 13
What are the main features of Umbrella for Cloud-Delivered Security?
A. Runs suspicious cloud applications in a sandbox environment
B. Handles 130B+ DNS requests daily with 99% uptime
C. Blocks malware, C2 callbacks and phishing over any port/protocol
D. Protects users against DDOS attacks
Correct Answer: C
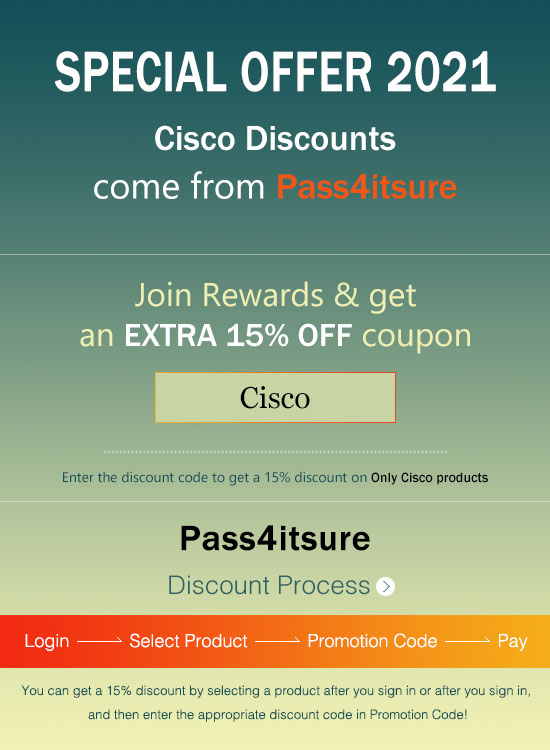
Pass4itsure Cisco exam dumps discount code share
Summarize:
[Q1-Q13] Free Cisco 700-765 pdf download https://drive.google.com/file/d/1mW2LCS8B9EjxKfVJjXv7Hs2L9SWBSrkQ/view?usp=sharing
Share all the resources: Latest Cisco 700-765 practice questions, latest Cisco 700-765 pdf dumps. The latest updated Cisco 700-765 dumps https://www.pass4itsure.com/700-765.html Study hard and practices a lot. This will help you prepare for the Cisco 700-765 exam. Good luck!
Related
Discover more from Exampass: Collection of Cisco (CCNA, CCNP, Meraki Solutions Specialist, CCDP...) exam questions and answers from Pass4itsure
Subscribe to get the latest posts sent to your email.
Written by Ralph K. Merritt
We are here to help you study for Cisco certification exams. We know that the Cisco series (CCNP, CCDE, CCIE, CCNA, DevNet, Special and other certification exams are becoming more and more popular, and many people need them. In this era full of challenges and opportunities, we are committed to providing candidates with the most comprehensive and comprehensive Accurate exam preparation resources help them successfully pass the exam and realize their career dreams. The Exampass blog we established is based on the Pass4itsure Cisco exam dump platform and is dedicated to collecting the latest exam resources and conducting detailed classification. We know that the most troublesome thing for candidates during the preparation process is often the massive amount of learning materials and information screening. Therefore, we have prepared the most valuable preparation materials for candidates to help them prepare more efficiently. With our rich experience and deep accumulation in Cisco certification, we provide you with the latest PDF information and the latest exam questions. These materials not only include the key points and difficulties of the exam, but are also equipped with detailed analysis and question-answering techniques, allowing candidates to deeply understand the exam content and master how to answer questions. Our ultimate goal is to help you study for various Cisco certification exams, so that you can avoid detours in the preparation process and get twice the result with half the effort. We believe that through our efforts and professional guidance, you will be able to easily cope with exam challenges, achieve excellent results, and achieve both personal and professional improvement. In your future career, you will be more competitive and have broader development space because of your Cisco certification.
Categories
2025 Microsoft Top 20 Certification Materials
- Microsoft Azure Administrator –> az-104 dumps
- Microsoft Azure Fundamentals –> az-900 dumps
- Data Engineering on Microsoft Azure –> dp-203 dumps
- Developing Solutions for Microsoft Azure –> az-204 dumps
- Microsoft Power Platform Developer –> pl-400 dumps
- Designing and Implementing a Microsoft Azure AI Solution –> ai-102 dumps
- Microsoft Power BI Data Analyst –> pl-300 dumps
- Designing and Implementing Microsoft DevOps Solutions –> az-400 dumps
- Microsoft Azure Security Technologies –> az-500 dumps
- Microsoft Cybersecurity Architect –> sc-100 dumps
- Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM) –> mb-910 dumps
- Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP) –> mb-920 dumps
- Microsoft Azure Data Fundamentals –> dp-900 dumps
- Microsoft 365 Fundamentals –> ms-900 dumps
- Microsoft Security Compliance and Identity Fundamentals –> sc-900 dumps
- Microsoft Azure AI Fundamentals –> ai-900 dumps
- Microsoft Dynamics 365: Finance and Operations Apps Solution Architect –> mb-700 dumps
- Microsoft 365 Certified: Enterprise Administrator Expert –> ms-102 dumps
- Microsoft 365 Certified: Collaboration Communications Systems Engineer Associate –> ms-721 dumps
- Endpoint Administrator Associate –> md-102 dumps

