Cisco Certification Exam Prep Materials
Cisco CCNA Exam Prep Material Download
Cisco CCT Exam Prep Material Download
- Cisco 010-151 Dumps PDF
- Cisco 100-490 Dumps PDF
- Cisco 100-890 Dumps PDF
- Tips: Beginning February 10, the CCT Certification 500-150 FLDTEC v1.0 exam will replace the 100-490, 010-151, and 100-890 exams.
Cisco CyberOps Exam Prep Material Download
Cisco DevNet Exam Prep Material Download
Cisco CCNP Exam Prep Material Download
- Cisco 300-410 Dumps PDF
- Cisco 300-415 Dumps PDF
- Cisco 300-420 Dumps PDF
- Cisco 300-425 Dumps PDF
- Cisco 300-430 Dumps PDF
- Cisco 300-435 Dumps PDF
- Cisco 300-440 Dumps PDF
- Cisco 300-510 Dumps PDF
- Cisco 300-515 Dumps PDF
- Cisco 300-535 Dumps PDF
- Cisco 300-610 Dumps PDF
- Cisco 300-615 Dumps PDF
- Cisco 300-620 Dumps PDF
- Cisco 300-630 Dumps PDF
- Cisco 300-635 Dumps PDF
- Cisco 300-710 Dumps PDF
- Cisco 300-715 Dumps PDF
- Cisco 300-720 Dumps PDF
- Cisco 300-725 Dumps PDF
- Cisco 300-730 Dumps PDF
- Cisco 300-735 Dumps PDF
- Cisco 300-810 Dumps PDF
- Cisco 300-815 Dumps PDF
- Cisco 300-820 Dumps PDF
- Cisco 300-835 Dumps PDF
Cisco CCIE Exam Prep Material Download
- Cisco 350-401 Dumps PDF
- Cisco 350-501 Dumps PDF
- Cisco 350-601 Dumps PDF
- Cisco 350-701 Dumps PDF
- Cisco 350-801 Dumps PDF
Cisco CCDE Exam Prep Material Download
Cisco Other Exam Prep Material Download
- Cisco 500-052 Dumps PDF
- Cisco 500-210 Dumps PDF
- Cisco 500-220 Dumps PDF
- Cisco 500-420 Dumps PDF
- Cisco 500-442 Dumps PDF
- Cisco 500-444 Dumps PDF
- Cisco 500-470 Dumps PDF
- Cisco 500-490 Dumps PDF
- Cisco 500-560 Dumps PDF
- Cisco 500-710 Dumps PDF
- Cisco 700-150 Dumps PDF
- Cisco 700-750 Dumps PDF
- Cisco 700-760 Dumps PDF
- Cisco 700-765 Dumps PDF
- Cisco 700-805 Dumps PDF
- Cisco 700-821 Dumps PDF
- Cisco 700-826 Dumps PDF
- Cisco 700-846 Dumps PDF
- Cisco 700-905 Dumps PDF
- Cisco 820-605 Dumps PDF
Fortinet Exam Dumps
fortinet nse4_fgt-6.4 dumps (pdf + vce)
fortinet nse4_fgt-6.2 dumps (pdf + vce)
fortinet nse5_faz-6.4 dumps (pdf + vce)
fortinet nse5_faz-6.2 dumps (pdf + vce)
fortinet nse5_fct-6.2 dumps (pdf + vce)
fortinet nse5_fmg-6.4 dumps (pdf + vce)
fortinet nse5_fmg-6.2 dumps (pdf + vce)
fortinet nse6_fml-6.2 dumps (pdf + vce)
fortinet nse6_fnc-8.5 dumps (pdf + vce)
fortinet nse7_efw-6.4 dumps (pdf + vce)
fortinet nse7_efw-6.2 dumps (pdf + vce)
fortinet nse7_sac-6.2 dumps (pdf + vce)
fortinet nse7_sdw-6.4 dumps (pdf + vce)
fortinet nse8_811 dumps (pdf + vce)
Valid Cisco 350-401 questions shared by Pass4itsure for helping to pass the Cisco 350-401 exam! Get the newest Pass4itsure Cisco 350-401 exam dumps with VCE and PDF here: https://www.pass4itsure.com/350-401.html (392 Q&As Dumps).
[Free PDF] Cisco 350-401 pdf Q&As https://drive.google.com/file/d/12eI_Nva_yrgBtQ2jmjc-9lE_rjhM9DIL/view?usp=sharing
Suitable for 350-401 complete Cisco learning pathway
The content is rich and diverse, and learning will not become boring. You can learn in multiple ways through the Cisco 350-401 exam.
- Download
- Answer practice questions, the actual Cisco 350-401 test
Cisco 350-401 Implementing and Operating Cisco Enterprise Network Core Technologies (ENCOR)
Free Cisco 350-401 dumps download
[PDF] Free Cisco 350-401 dumps pdf download https://drive.google.com/file/d/12eI_Nva_yrgBtQ2jmjc-9lE_rjhM9DIL/view?usp=sharing
Pass4itsure offers the latest Cisco 350-401 practice test free of charge 1-13
QUESTION 1
How does the RIB differ from the FIB?
A. The RIB is used to create network topologies and routing tables. The FIB is a list of routes to particular network
destinations.
B. The FIB includes many routes a single destination. The RIB is the best route to a single destination.
C. The RIB includes many routes to the same destination prefix. The FIB contains only the best route
D. The FIB maintains network topologies and routing tables. The RIB is a Iist of routes to particular network
destinations.
Correct Answer: A
QUESTION 2
Which statement about Cisco Express Forwarding is true?
A. It uses a fast cache that is maintained in a router data plane.
B. maintains two tables in the data plane the FIB and adjacency table.
C. It makes forwarding decisions by a process that is scheduled through the IOS scheduler.
D. The CPU of a router becomes directly involved with packet-switching decisions.
Correct Answer: B
Cisco Express Forwarding (CEF) provides the ability to switch packets through a device in a very quick and efficient way
while also keeping the load on the router\\’s processor low. CEF is made up of two different main components: the
Forwarding Information Base (FIB) and the Adjacency Table. These are automatically updated at the same time as the
routing table. The Forwarding Information Base (FIB) contains destination reachability information as well as next hop
information. This information is then used by the router to make forwarding decisions. The FIB allows for very efficient
and easy lookups. Below is an example of the FIB table: The adjacency table is tasked with maintaining the layer 2 nexthop information for the FIB. An example of the adjacency table is shown below:
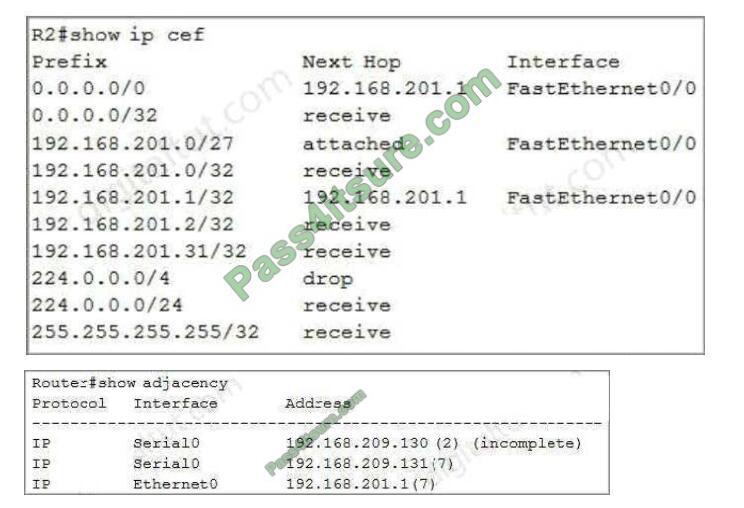
It uses a fast cache that is maintained in a router data plane\\’ fast cache is only used when fast switching is enabled
while CEF is disabled.
QUESTION 3
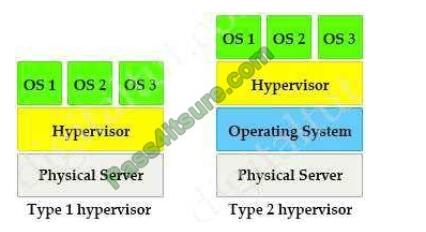
Which statement explains why Type 1 hypervisor is considered more efficient than Type 2 hypervisor?
A. Type 1 hypervisor runs directly on the physical hardware of the host machine without relying on the underlying OS.
B. Type 1 hypervisor enables other operating systems to run on it.
C. Type 1 hypervisor relics on the existing OS of the host machine to access CPU, memory, storage, and network
resources.
D. Type 1 hypervisor is the only type of hypervisor that supports hardware acceleration techniques.
Correct Answer: A
There are two types of hypervisors: type 1 and type 2 hypervisor. In type 1 hypervisor (or native hypervisor), the
hypervisor is installed directly on the physical server. Then instances of an operating system (OS) are installed on the
hypervisor. Type 1 hypervisor has direct access to the hardware resources. Therefore they are more efficient than
hosted architectures. Some examples of type 1 hypervisor are VMware vSphere/ESXi, Oracle VM Server, KVM and
Microsoft Hyper-V.
In contrast to type 1 hypervisor, a type 2 hypervisor (or hosted hypervisor) runs on top of an operating system and not
the physical hardware directly. answer \\’Type 1 hypervisor runs directly on the physical hardware of the host machine
without relying on the underlying OS\\’ big advantage of Type 2 hypervisors is that management console software is not
required. Examples of type 2 hypervisor are VMware Workstation (which can run on Windows, Mac and Linux) or
Microsoft Virtual PC (only runs on Windows).
QUESTION 4
What is the main function of VRF-lite?
A. To connect different autonomous systems together to share routes
B. To allow devices to use labels to make Layer 2 Path decisions
C. To route IPv6 traffic across an IPv4 backbone
D. To segregate multiple routing tables on a single device
Correct Answer: D
QUESTION 5
What mechanism does PIM use to forward multicast traffic?
A. PIM sparse mode uses a pull model to deliver multicast traffic.
B. PIM dense mode uses a pull model to deliver multicast traffic.
C. PIM sparse mode uses receivers to register with the RP.
D. PIM sparse mode uses a flood and prune model to deliver multicast traffic.
Correct Answer: A
PIM dense mode (PIM-DM) uses a push model to flood multicast traffic to every corner of the network. This push model
is a brute-force method of delivering data to the receivers. This method would be efficient in certain deployments in
which there are active receivers on every subnet in the network. PIM-DM initially floods multicast traffic throughout the
network. Routers that have no downstream neighbors prune the unwanted traffic. This process repeats every 3 minutes.
PIM Sparse Mode (PIM-SM) uses a pull model to deliver multicast traffic. Only network segments with active receivers
that have explicitly requested the data receive the traffic. PIM-SM distributes information about active sources by
forwarding data packets on the shared tree. Because PIM-SM uses shared trees (at least initially), it requires the use of
an RP. The RP must be administratively configured in the network. Answer C seems to be correct but it is not, PIM
spare mode uses sources (not receivers) to register with the RP. Sources register with the RP, and then data is
forwarded down the shared tree to the receivers. Reference: Selecting MPLS VPN Services Book, page 193
QUESTION 6
IS OSPF, which LAS type is responsible for pointing to the ASBR router?
A. type 1
B. type 2
C. type 3
D. type 4
Correct Answer: D
QUESTION 7
Why is an AP joining a different WLC than the one specified through option 43?
A. The WLC is running a different software version.
B. The AP is joining a primed WLC.
C. The AP multicast traffic unable to reach the WLC through Layer 3.
D. The APs broadcast traffic is unable to reach the WLC through Layer 2.
Correct Answer: B
QUESTION 8
Which two entities are Type 1 hypervisors? (Choose two.)
A. Oracle VM VirtualBox
B. Microsoft Hyper-V
C. VMware server
D. VMware ESX
E. Microsoft Virtual PC
Correct Answer: BD
A bare-metal hypervisor (Type 1) is a layer of software we install directly on top of a physical server and its underlying
hardware. There is no software or any operating system in between, hence the name bare-metal hypervisor. A Type 1
hypervisor is proven in providing excellent performance and stability since it does not run inside Windows or any other
operating system. These are the most common type 1 hypervisors:
+
VMware vSphere with ESX/ESXi
+
KVM (Kernel-Based Virtual Machine)
+
Microsoft Hyper-V
+
Oracle VM
+
Citrix Hypervisor (formerly known as Xen Server)
Reference: https://phoenixnap.com/kb/what-is-hypervisor-type-1-2
QUESTION 9
A network administrator is preparing a Python script to configure a Cisco IOS XE-based device on the network. The
administrator is worried that colleagues will make changes to the device while the script is running.
Which operation of the ncclient manager prevents colleagues from making changes to the devices while the script is
running?
A. m.lock(config=\\’running\\’)
B. m.lock(target=\\’running\\’)
C. m.freeze(target=\\’running\\’)
D. m.freeze(config=\\’running\\’)
Correct Answer: B
QUESTION 10
Which component of the Cisco Cyber Threat Defense solution provides user and flow context analysis?
A. Cisco Firepower and FireSIGHT
B. Cisco Stealthwatch system
C. Advanced Malware Protection
D. Cisco Web Security Appliance
Correct Answer: B
The goal of the Cyber Threat Defense solution is to introduce a design and architecture that can help facilitate the
discovery, containment, and remediation of threats once they have penetrated into the network interior. Cisco Cyber
Threat Defense version 2.0 makes use of several solutions to accomplish its objectives:
* NetFlow and the Lancope StealthWatch System
1.
Broad visibility
2.
User and flow context analysis
3.
Network behavior and anomaly detection
4.
Incident response and network forensics
* Cisco FirePOWER and FireSIGHT
1.
Real-time threat management
2.
Deeper contextual visibility for threats bypassing the perimeters ?URL control
* Advanced Malware Protection (AMP)
1.
Endpoint control with AMP for Endpoints
2.
Malware control with AMP for networks and content
* Content Security Appliances and Services
1.
Cisco Web Security Appliance (WSA) and Cloud Web Security (CWS)
2.
Dynamic threat control for web traffic
3.
Outbound URL analysis and data transfer controls
4.
Detection of suspicious web activity
5.
Cisco Email Security Appliance (ESA)
6.
Dynamic threat control for email traffic
7.
Detection of suspicious email activity
* Cisco Identity Services Engine (ISE)
1.
User and device identity integration with Lancope StealthWatch
2.
Remediation policy actions using pxGrid
Reference: https://www.cisco.com/c/dam/en/us/td/docs/security/network_security/ctd/ctd2-0/design_guides/ctd_20_cvd_guide_jul15.pdf
QUESTION 11
What is used to measure the total output energy of a Wi-Fi device?
A. dBi
B. EIRP
C. mW
D. dBm
Correct Answer: C
Output power is measured in mW (milliwatts). answer \\’dBi\\’ milliwatt is equal to one thousandth (10-3) of a watt.
QUESTION 12
What does Call Admission Control require the client to send in order to reserve the bandwidth?
A. SIP flow information
B. Wi-Fi multimedia
C. traffic specification
D. VoIP media session awareness
Correct Answer: D
QUESTION 13
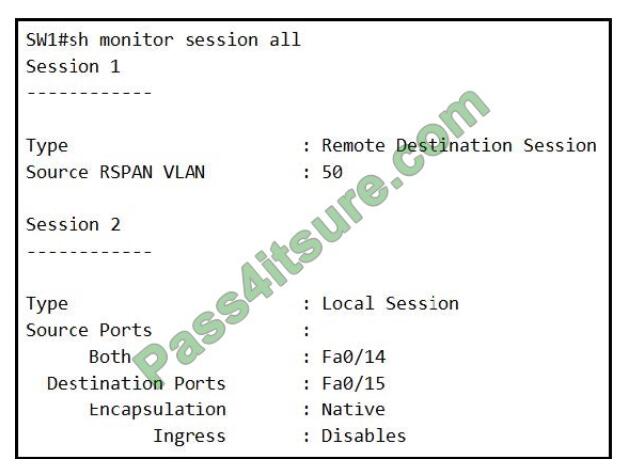
Refer to the exhibit. An engineer configures monitoring on SW1 and enters the show command to verify operation. What
does the output confirm?
A. SPAN session 1 monitors activity on VLAN 50 of a remote switch
B. SPAN session 2 only monitors egress traffic exiting port FastEthernet 0/14.
C. SPAN session 2 monitors all traffic entering and exiting port FastEthernet 0/15.
D. RSPAN session 1 is incompletely configured for monitoring
Correct Answer: D
Summarize:
[Q1-Q13] Free Cisco 350-401 pdf download https://drive.google.com/file/d/12eI_Nva_yrgBtQ2jmjc-9lE_rjhM9DIL/view?usp=sharing
Share all the resources: Latest Cisco 350-401 practice questions, latest Cisco 350-401 pdf dumps. The latest updated Cisco 350-401 dumps https://www.pass4itsure.com/350-401.html Study hard and practices a lot. This will help you prepare for the Cisco 350-401 exam. Good luck!
Related
Discover more from Exampass: Collection of Cisco (CCNA, CCNP, Meraki Solutions Specialist, CCDP...) exam questions and answers from Pass4itsure
Subscribe to get the latest posts sent to your email.
Written by Ralph K. Merritt
We are here to help you study for Cisco certification exams. We know that the Cisco series (CCNP, CCDE, CCIE, CCNA, DevNet, Special and other certification exams are becoming more and more popular, and many people need them. In this era full of challenges and opportunities, we are committed to providing candidates with the most comprehensive and comprehensive Accurate exam preparation resources help them successfully pass the exam and realize their career dreams. The Exampass blog we established is based on the Pass4itsure Cisco exam dump platform and is dedicated to collecting the latest exam resources and conducting detailed classification. We know that the most troublesome thing for candidates during the preparation process is often the massive amount of learning materials and information screening. Therefore, we have prepared the most valuable preparation materials for candidates to help them prepare more efficiently. With our rich experience and deep accumulation in Cisco certification, we provide you with the latest PDF information and the latest exam questions. These materials not only include the key points and difficulties of the exam, but are also equipped with detailed analysis and question-answering techniques, allowing candidates to deeply understand the exam content and master how to answer questions. Our ultimate goal is to help you study for various Cisco certification exams, so that you can avoid detours in the preparation process and get twice the result with half the effort. We believe that through our efforts and professional guidance, you will be able to easily cope with exam challenges, achieve excellent results, and achieve both personal and professional improvement. In your future career, you will be more competitive and have broader development space because of your Cisco certification.
Categories
2025 Microsoft Top 20 Certification Materials
- Microsoft Azure Administrator –> az-104 dumps
- Microsoft Azure Fundamentals –> az-900 dumps
- Data Engineering on Microsoft Azure –> dp-203 dumps
- Developing Solutions for Microsoft Azure –> az-204 dumps
- Microsoft Power Platform Developer –> pl-400 dumps
- Designing and Implementing a Microsoft Azure AI Solution –> ai-102 dumps
- Microsoft Power BI Data Analyst –> pl-300 dumps
- Designing and Implementing Microsoft DevOps Solutions –> az-400 dumps
- Microsoft Azure Security Technologies –> az-500 dumps
- Microsoft Cybersecurity Architect –> sc-100 dumps
- Microsoft Dynamics 365 Fundamentals Customer Engagement Apps (CRM) –> mb-910 dumps
- Microsoft Dynamics 365 Fundamentals Finance and Operations Apps (ERP) –> mb-920 dumps
- Microsoft Azure Data Fundamentals –> dp-900 dumps
- Microsoft 365 Fundamentals –> ms-900 dumps
- Microsoft Security Compliance and Identity Fundamentals –> sc-900 dumps
- Microsoft Azure AI Fundamentals –> ai-900 dumps
- Microsoft Dynamics 365: Finance and Operations Apps Solution Architect –> mb-700 dumps
- Microsoft 365 Certified: Enterprise Administrator Expert –> ms-102 dumps
- Microsoft 365 Certified: Collaboration Communications Systems Engineer Associate –> ms-721 dumps
- Endpoint Administrator Associate –> md-102 dumps

